A lil about burp suite professional training
Burp Suite is the world's most widely used web application security testing software. Burp comes as two versions - Burp Suite Professional for hands-on testers.
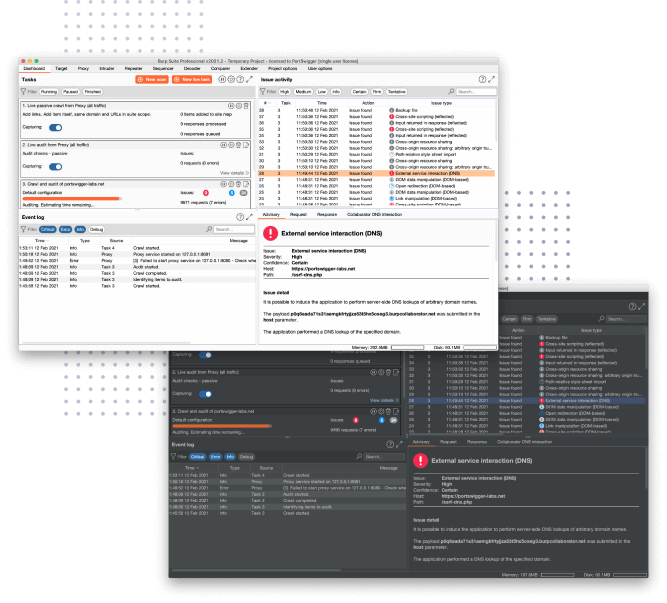
Burp Suite Professional is an advanced set of tools for testing web security - all within a single product. From a basic intercepting proxy to a cutting-edge vulnerability scanner, with Burp Suite Pro, the right tool is never more than a click away.
powerful automation gives you more opportunity to do what you do best, while Burp Suite handles low-hanging fruit. Advanced manual tools will then help you identify your target's more subtle blind spots.
Burp Suite Pro can be used to test for the whole OWASP Top 10. The work of PortSwigger's world-leading research team guides Burp Suite's development, and new capabilities are added with each new update. Automatically harvest low-hanging fruit
At Burp Suite's heart lies the web vulnerability scanner. This is the same powerful scanner trusted by many of the world's largest organizations. It's capable of both passive and active analysis.
Find more vulnerabilities, faster
Automate and save time
Smart automation works in concert with expert-designed manual tools, to save you time. Optimize your workflow, and do more of what you do best.
Increase scan coverage
Burp Scanner is designed to test feature rich modern web applications. Scan JavaScript, test APIs, and record complex authentication sequences.
Minimize false positives
Ultra reliable out-of-band application security testing (OAST) can find many otherwise invisible vulnerabilities. Burp Suite Professional makes it easy.
Syllabus
Contact me for any questions at: atuljetli (at) gmail (dot) com
The following 3 days live training (might change depending upon tools changes) describes what you will learn and master the burp suite.
DAY 1
First warming up with the proxy interception, we will move to the following to gain more fluency using the tool.
- Introduction: some important details and advice about the course and training with burp suite.
- Lab environments configuration, Burp CA certificate for SSL/TLS,
- Interceptor proxy with filters, Invisible proxying for non-proxy aware clients
- Host-header rewriting, live traffic modifications, match & replace rules, Response modification and Web sockets streaming capture and replay
- Intercepting mobile devices traffic with Burp Suite – iPhone
- Repeater: replying with repeater in request one by one
- Intruder: Advanced Intruder module attacks,Payloads placement for multiple injections, Sniper attacks, Battering arm, pitch fork, Cluster Bomb
- Data extraction with match and grep, Custom exploits with intruder
- Response header manipulation, Attacking hidden form fields
- All payload types explained practically
- Attacks users – Insecure direct object reference
DAY 2
- Burp Macros and session handling rules: Managing CSRF tokens to login automatically, many rules in session handling, authentication management using session handling rules
- Important extensions: Turbo intruder, Logger++, hackverter, backslash powered scanner, auto-repeater and many useful extensions explained practically
- Burp Extender APIs
- Anti-CSRF token attacks
- Generating PoC for self submitting CSRF form
- Sequencer: session token analysis with live and manual capture
DAY 3
- Project options and user options: make various configurations for project of penetration testing and user settings.
- Preparing burp suite for pentest engagement
- Target site map: setting up site map for scope and issue definitions
- Scan and live audit: auditing the target live as we capture the request or visit the target site manually
- Target crawl and audit: crawling the target and auditing it as we go simultaneously
- Dashboard: the central view of what the burp is doing at one place
- Engagement tools
- Burp Collaborator
- ClickBandit
- Burp Infiltrator attacks
Bonus: there will be a final security test in one shot to the live target to demonstrate how a penetration tester and or bug bounty hunter will use this ahead.
Frequently Asked Questions
Can I get a refund if I'm unhappy with my purchase?
If you are unsatisfied with your coaching, reach out to me to see if your purchase is eligible for a refund.
How do I schedule my appointment?
Upon purchasing coaching, you'll receive further instructions on how to book a time for your appointment.
Can I purchase coaching more than once?
Absolutely! If you find yourself in need of coaching more than once, simply purchase the coaching again.
